Quantum-secure communication
Quantum-secure communication is a technology that safeguards information transmission by utilizing the principles of quantum mechanics. When applied to walkie-talkies, it creates quantum-secure intercoms, adding a theoretically "unbreakable" lock to traditional voice communications
3/2/20262 min read
Quantum-secure communication is a technology that safeguards information transmission by utilizing the principles of quantum mechanics. When applied to walkie-talkies, it creates quantum-secure intercoms, adding a theoretically "unbreakable" lock to traditional voice communications.
Simply put, this technology does not transmit voice directly via quantum signals. Instead, it uses quantum technology to generate an uncrackable "key" for encrypting conversations.
Core Principle: Why is it immune to eavesdropping?
The security of quantum encryption is rooted in the unique properties of quantum mechanics:
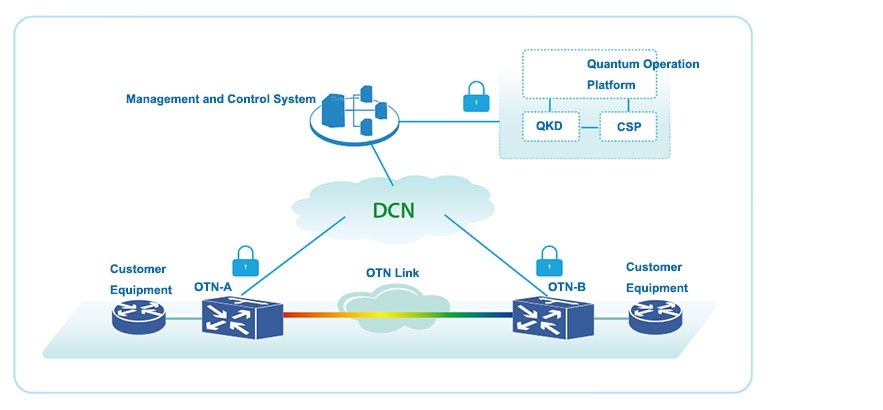
Quantum Key Distribution (QKD): This is the most widely used technical approach currently. Before communication begins, the intercoms negotiate and generate an encryption key through a quantum channel (usually optical fiber).
The "Uncertainty" and "No-Cloning" Theorems: The carrier of this key is a single photon. According to quantum physics, any attempt to eavesdrop on or measure a photon will inevitably alter its state. This is like a "quantum safe"—if anyone tries to peek, the safe will immediately trigger an alarm and leave a trace.
One-Time Pad: A new, completely random key is generated every time a call is established. Once the call ends, the key is immediately discarded and a new one is used for the next call. This makes "perfect secrecy" possible; even if a hacker intercepts the ciphertext, they cannot decipher it without the key.
Application in Walkie-Talkies: Functions and Advantages
Integrating quantum encryption technology into walkie-talkies results in the following product forms and advantages:
Product Form: It typically consists of a quantum security TF card, a quantum-secure intercom terminal (a dedicated walkie-talkie or a mobile app), and a cloud-based quantum security service platform.
Core Functions:
End-to-End Encryption: The entire communication link, from one intercom to another, is protected by the quantum key.
Identity Authentication: It ensures that only authenticated, legitimate terminals can join the communication network, preventing identity spoofing.
Main Advantages:
Eavesdropping Prevention: It fundamentally eliminates the risk of call content being intercepted and deciphered by third parties.
High Security Level: It is especially suitable for scenarios with extremely high communication security requirements, such as government affairs, public security, and large-scale event security.
Real-World Applications and Development
Quantum-secure intercoms have moved from theory to practical application. In China, they have been widely deployed in conjunction with 5G networks:
Major Event Support: During international mega-events like the 2022 Beijing Winter Olympics and the 2023 Hangzhou Asian Games, quantum-secure intercoms undertook core communication security tasks, ensuring the safety of command and dispatch instructions.
Local Cultural Events: For example, in Zhangzhou, Fujian, the quantum-secure intercom technology provided by China Telecom offered full-process communication support for cultural performances like "Xixi Minnan," ensuring command security in complex, crowded environments.
Industry Integration: In Guangdong, quantum encryption technology has been integrated with the power emergency command system, achieving "quantum-secure broadband and narrowband integrated communication." This integration of high-security quantum encryption with 5G public networks and 800M private network walkie-talkies has enhanced the efficiency and security of emergency responses.
Applying quantum-secure communication to walkie-talkies provides a "conditionally secure" communication method for command and dispatch in critical fields. It is one of the highest-level communication security safeguards currently available.
Chenghui International Park ,Nan 'an,Quanzhou ,Fujian ,China 362300.
Your Secure Communication Is Our Mission


allyxubin
ally@akl-tech.com anson@akl-tech.com
© 2024-2025 All rights reserved. AKL Technology Co.,Limited All Rights Reserved.
POC Radio
DMR Radio
Analog Radio
Radio Accessories
86-15859775920
